Mar. 04, 2026


16 minutes read

Share this article
Last Updated March 2026
Healthcare providers, universities, and edtech companies routinely handle data that falls under not one but two federal privacy laws. Understanding the precise differences between HIPAA and FERPA — who each applies to, what data they protect, how enforcement works, and when the two frameworks overlap — is essential for any organization operating at the intersection of health and education. This guide cuts through the legal jargon so your team can build compliant systems with confidence.
50M+ Student records protected by FERPA at federally funded schools
Both HIPAA and FERPA are federal laws designed to safeguard sensitive personal data — but they operate in entirely different sectors and were created to solve different problems.
Enacted in 1996 and significantly expanded by the HITECH Act (2009), HIPAA sets national standards for protecting Protected Health Information (PHI). Its Privacy Rule, Security Rule, and Breach Notification Rule collectively govern how covered entities — hospitals, clinics, insurers, and their business associates — must collect, store, transmit, and disclose patient data. Beyond paper records, HIPAA applies to electronic PHI (ePHI) held in any digital system, from cloud databases to mobile health apps.
Signed into law in 1974, FERPA protects the privacy of student education records at institutions that receive federal Department of Education funding — virtually every public school, college, and university in the United States. FERPA gives students (or their parents, if under 18) the right to inspect their records, request corrections, and control who receives their information. For organizations building edtech platforms, FERPA is the primary compliance framework to understand.
Key Takeaway:
HIPAA governs health data in healthcare settings. FERPA governs academic records in educational settings. When an institution straddles both worlds — such as a university campus health clinic — both may apply, and knowing which takes precedence matters.
The table below captures the most critical dimensions of difference between the two laws.
| Dimension | HIPAA | FERPA |
|---|---|---|
| Full Name | Health Insurance Portability & Accountability Act | Family Educational Rights & Privacy Act |
| Year Enacted | 1996 (expanded 2009 via HITECH) | 1974 |
| Primary Sector | Healthcare | Education |
| Who Must Comply | Covered entities (hospitals, clinics, insurers, clearinghouses) and their Business Associates | Educational institutions receiving federal funds (K-12 schools, colleges, universities) |
| Protected Data | Protected Health Information (PHI): diagnoses, medications, billing, insurance, test results | Education records: grades, transcripts, enrollment data, financial aid, disciplinary records |
| Consent Requirement | Written authorization required for most disclosures; exceptions for treatment, payment, operations | Written consent required to release records; exceptions for school officials, emergencies, court orders |
| Individual Rights | Access, amendment, accounting of disclosures, right to restrict | Inspect & review records, request amendment, control disclosure |
| Enforcement Body | HHS Office for Civil Rights (OCR) | Dept. of Education — Student Privacy Policy Office (SPPO) |
| Maximum Civil Penalty | $1.9M per violation category per year | Loss of federal funding (no per-violation fine) |
| Criminal Penalties | Up to 10 years imprisonment for intentional wrongful disclosure | None directly; civil remedies available |
| Breach Notification | Required within 60–72 hours to individuals and HHS | No mandatory federal breach notification (state laws may apply) |
| Technical Safeguards | Mandatory under Security Rule: encryption, access controls, audit logs | No explicit technical requirements; “reasonable measures” standard |
PHI is any individually identifiable information related to an individual’s past, present, or future health condition, treatment, or payment for healthcare. HIPAA identifies 18 distinct identifiers — including names, geographic data smaller than a state, Social Security numbers, and biometric identifiers — whose combination with health data makes information “protected.”
Electronic PHI (ePHI) is governed by HIPAA’s Security Rule, which mandates administrative, physical, and technical safeguards. For organizations managing cloud infrastructure, this typically means encryption at rest and in transit, role-based access control, and comprehensive audit logging. A single unencrypted laptop containing patient records constitutes a reportable breach.
FERPA covers “education records” — a broad category defined as records directly related to a student and maintained by an institution or its authorized agents. This includes grades, transcripts, enrollment status, financial aid information, disciplinary files, and even certain student health records held by a campus health center (not a separately operating clinic).
The overlap zone: When a university maintains student health records in a student’s file, those records fall under FERPA, not HIPAA, even though they contain health information. Only when a campus clinic operates as a separate HIPAA-covered entity do those records migrate to HIPAA jurisdiction. This distinction trips up many compliance teams.
HIPAA does not cover de-identified data (information stripped of all 18 identifiers) or employment records held by an employer. FERPA does not protect alumni giving records, general institutional research data unconnected to individual students, or records maintained solely by a law enforcement unit.
The two laws take very different approaches to enforcement — HIPAA uses a tiered financial penalty system with criminal provisions, while FERPA relies primarily on the threat of losing federal funding.
HIPAA enforcement has intensified significantly. HHS OCR collected over $135 million in HIPAA penalties between 2016 and 2023, with major settlements reaching $16 million (Anthem, 2018) and $10.8 million (Memorial Healthcare, 2017). The most common violations involve unauthorized access, missing risk analyses, and inadequate Business Associate Agreements.
For FERPA, the Department of Education rarely escalates to funding withdrawal — but the reputational and institutional damage from an SPPO finding is significant. Additionally, many states (including California, New York, and Texas) have enacted their own student data privacy laws with direct financial penalties that fill the gap left by federal FERPA enforcement.
$1.9M Maximum annual HIPAA civil penalty per violation category
Universities are the most common setting in which both laws apply simultaneously. A large research university might operate a hospital (HIPAA), a medical school (HIPAA + FERPA), undergraduate health services (FERPA), and an edtech platform for health science students (FERPA, potentially HIPAA for real patient data used in training).
FERPA includes a specific exemption: records that are “treatment records” for post-secondary students — maintained by healthcare professionals and used only for treatment — are excluded from FERPA’s definition of education records and therefore fall under HIPAA. This is the “treatment records exception,” and correctly applying it requires careful documentation of how records are maintained and used.
| Scenario | Which Law Applies | Rationale |
|---|---|---|
| University hospital treating student patients | HIPAA | Hospital is a covered entity; records are clinical, not academic |
| Campus health clinic records filed in student folder | FERPA | Records maintained as part of education record; FERPA takes precedence |
| Medical school student accessing real patient EHR for training | HIPAA | Real patient PHI; student is functioning as a workforce member |
| K-12 school sharing student health allergy list with cafeteria | FERPA | K-12 schools aren’t HIPAA covered entities; FERPA governs school records |
| Telehealth startup serving adult patients | HIPAA | Campus health clinic records filed in the student’s folder |
Whether your organization needs to comply with one or both laws, the following technical and organizational practices form the foundation of a defensible compliance posture. Coderio’s Digital Security Studio regularly helps healthcare and education clients implement these frameworks.
72 hrs Maximum window to report a HIPAA data breach to HHS
Organizations subject to HIPAA or FERPA rely on a growing set of compliance technologies. The chart below shows the primary compliance investment categories among U.S. healthcare and education IT organizations based on industry survey data.
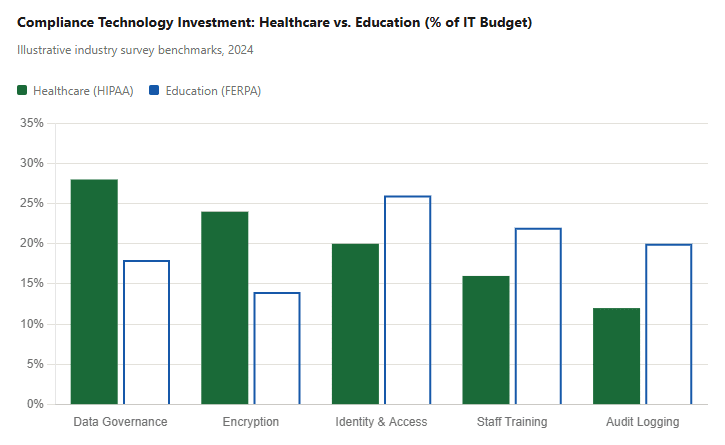
The data reflects a structural difference: HIPAA mandates specific technical controls (driving higher spend on encryption and data governance), while FERPA’s “reasonable measures” standard pushes more educational institutions to invest in identity management and training as their primary compliance lever. Organizations building digital transformation programs in either sector need to account for these baseline compliance investments from day one.
For engineering teams, HIPAA and FERPA aren’t abstract legal concepts — they are hard technical requirements that influence every layer of the stack, from database schema design to API architecture to vendor selection. Ignoring them during development means expensive retrofits later, and in the worst case, a breach that triggers federal enforcement.
The most costly mistake development teams make is treating compliance as a post-launch checklist rather than a design constraint. HIPAA’s Security Rule mandates specific technical safeguards for any system that touches ePHI: encryption at rest and in transit, unique user identification, automatic logoff, audit controls, and integrity mechanisms to detect unauthorized data alteration. These are not features you add in a later sprint — they are foundational architectural decisions.
For FERPA, the technical requirements are less prescriptive (“reasonable measures” is the standard), but the practical implications are similar. Any platform that stores, processes, or transmits student education records needs role-based access control, data segregation between student cohorts, and clear audit trails showing who accessed what and when.
HIPAA-compliant database design requires more than encryption. Development teams must implement field-level access controls so that, for example, a billing module can read insurance claim data but cannot access clinical notes. PHI must be logically or physically separated from non-regulated data. Backup and disaster recovery systems must apply the same safeguards as primary systems — an encrypted primary database with an unencrypted backup is still a HIPAA violation.
Data residency decisions also carry compliance weight. HIPAA does not prohibit storing PHI outside the United States, but doing so complicates Business Associate Agreements and introduces conflict-of-laws risks with international data protection frameworks such as the GDPR. Most healthcare clients specify domestic data residency as a contractual requirement. For teams building on cloud infrastructure, this means selecting region-locked storage from day one rather than reconfiguring it after a compliance audit.
Modern healthcare and education platforms are API-driven — EHR integrations, LMS connectors, identity providers, analytics pipelines. Every API endpoint that exposes PHI or student records is a potential source of violations. HIPAA-compliant APIs require OAuth 2.0 or equivalent authorization, mutual TLS for service-to-service communication, rate limiting to prevent bulk data extraction, and payload-level audit logging that captures not just that a request was made, but what data was returned.
Third-party integrations introduce another layer of risk. Under HIPAA, every vendor that receives PHI through an integration must sign a Business Associate Agreement before data flows to them, including analytics tools, error-tracking platforms, and cloud logging services. Under FERPA, the same principle applies through the “school official” exception: a vendor must have a documented legitimate educational interest before student data can be shared with them programmatically. Development teams that wire up third-party SDKs without legal review of the data-sharing relationship create compliance exposure that no technical control can retroactively fix.
Both laws require organizations to know exactly who accessed regulated data and when. This shapes authentication architecture significantly. Shared login credentials are incompatible with HIPAA’s unique user identification requirement. Session management must enforce automatic logoff after defined inactivity periods. Privileged access to production databases containing PHI or education records must be mediated through a Privileged Access Management (PAM) solution, not direct database credentials distributed across the team.
For mobile app development in healthcare and education, these requirements extend to the device layer: apps handling PHI must implement certificate pinning, secure local storage (no plaintext caching of sensitive fields), and remote wipe capability if the device is lost or compromised.
One of the most overlooked compliance risks in software development is test data. Using real patient records or real student data in development and staging environments is a common HIPAA and FERPA violation — and it happens frequently when engineers copy production snapshots to test new features. Compliant development pipelines require synthetic data generation or properly de-identified datasets for non-production environments, with controls preventing production PHI from flowing into lower environments.
CI/CD pipelines themselves must be hardened. Secrets management (API keys, database credentials, encryption keys) must use a dedicated vault rather than environment variables or version-controlled config files. Automated software testing pipelines should include security scans — SAST, DAST, and dependency vulnerability checks — as mandatory gates before any release touching regulated data.
HIPAA’s Security Rule requires audit controls: hardware, software, and procedural mechanisms that record and examine activity in information systems containing PHI. In practice, this means structured application logging, centralized log aggregation with tamper-evident storage, and automated alerting for anomalous access patterns. A HIPAA-compliant logging architecture should be able to answer, within hours of a suspected breach: who accessed the data, from where, at what time, and what specific records were involved.
Building this capability into a platform from the start — rather than bolting on a SIEM after an incident — is one of the highest-leverage investments an engineering team can make. It reduces breach investigation time from weeks to hours and is often the difference between a self-reported incident with reduced penalties and a discovered violation with maximum enforcement exposure.
Implementation Tip: When scoping a new feature that touches regulated data, require a one-page Privacy Impact Assessment (PIA) before engineering begins. It takes 30 minutes, forces the team to identify the applicable law, the data elements involved, the access controls needed, and the third-party integrations required — and it creates a documented compliance decision trail that regulators view favorably during audits.
Both HIPAA and FERPA were written decades before cloud computing, AI, and mobile-first architectures became standard. Organizations now face compliance challenges that the original laws never anticipated.
Training AI models on PHI or student data requires careful data governance. De-identification under HIPAA’s Safe Harbor or Expert Determination methods is necessary before using health data for model training. For FERPA, sharing student data with AI vendors must be governed by legitimate educational interest exceptions or explicit consent — generic vendor data-sharing agreements often fail to meet this standard. Coderio’s ML & AI Studio builds privacy-by-design pipelines for regulated sectors.
HIPAA’s Security Rule applies to ePHI wherever it resides — on-premises, in the cloud, or in a hybrid environment. Major cloud providers (AWS, Azure, GCP) offer Business Associate Agreements and HIPAA-eligible services, but configuration remains the organization’s responsibility. A misconfigured S3 bucket exposing patient data remains a HIPAA breach, regardless of the cloud provider’s compliance certifications. For cloud application development, compliance requirements must be baked into infrastructure-as-code from day one.
FERPA’s School Official exception — which allows sharing student data with vendors providing services to the institution — has been stretched to its limits by the proliferation of LMS platforms, assessment tools, and AI tutoring software. Each vendor relationship requires a written agreement establishing the vendor as a “school official” with a legitimate educational interest. Institutions that fail to document these relationships risk FERPA violations even when the vendor’s use of data is benign.
HIPAA protects individually identifiable health information held by healthcare providers, insurers, and clearinghouses, as well as their business associates. FERPA protects education records maintained by schools receiving federal funding. The core difference lies in sector and data type: HIPAA governs clinical health data; FERPA governs academic records.
Yes, most commonly at universities with campus health services or medical schools. In overlap scenarios, FERPA generally takes precedence for student health records maintained as part of an education record. Separately operated campus clinics functioning as HIPAA covered entities are governed by HIPAA for those clinical records.
FERPA applies to any educational institution — public or private — that receives funds from the U.S. Department of Education. This includes virtually all colleges and universities (which participate in federal student aid programs) and most K-12 schools. A small number of private schools that accept no federal funding are not subject to FERPA, though state privacy laws may still apply.
Any unauthorized acquisition, access, use, or disclosure of unsecured PHI that compromises the privacy or security of that information is presumed to be a breach — unless the covered entity can demonstrate via a four-factor risk assessment that the probability of PHI compromise is low. Notifications must reach affected individuals within 60 days, HHS within 60 days (or 72 hours for “significant” breaches under newer guidance), and media outlets if more than 500 residents of a state are affected.
Yes, if a SaaS vendor creates, receives, maintains, or transmits PHI on behalf of a covered entity, they are a Business Associate and must sign a BAA. This includes cloud storage providers, analytics platforms, communication tools, and any software that processes patient data. Deploying SaaS tools that touch PHI without a signed BAA is one of the most common — and costliest — HIPAA violations.
Coderio’s nearshore engineering teams have deep expertise in compliance-ready architectures for healthcare and education clients. Talk to Our Team
If you found this guide useful, these related articles from Coderio dive deeper into compliance, data governance, and secure software development:
Data Governance Studio: Tailored Solutions for Regulated Industries
SecurityDigital Security Studio: Securing Your Business, One Layer at a Time
Healthcare TechSoftware Development for Healthcare: What Compliance-First Engineering Looks Like
EdTechEdTech Software Development: Building FERPA-Ready Learning Platforms

As the Vice President of Sales, Michael leads revenue growth initiatives in the US and LATAM markets. Michael holds a bachelor of arts and a bachelor of Systems Engineering, a master’s degree in Capital Markets, an MBA in Business Innovation, and is currently studying for his doctorate in Finance. His ability to identify emerging trends, understand customer needs, and deliver tailored solutions that drive value and foster long-term partnerships is a testament to his strategic vision and expertise.

As the Vice President of Sales, Michael leads revenue growth initiatives in the US and LATAM markets. Michael holds a bachelor of arts and a bachelor of Systems Engineering, a master’s degree in Capital Markets, an MBA in Business Innovation, and is currently studying for his doctorate in Finance. His ability to identify emerging trends, understand customer needs, and deliver tailored solutions that drive value and foster long-term partnerships is a testament to his strategic vision and expertise.
Accelerate your software development with our on-demand nearshore engineering teams.